Auditing NQ Contacts Backup & Restore 1.1
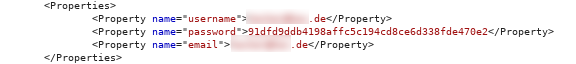
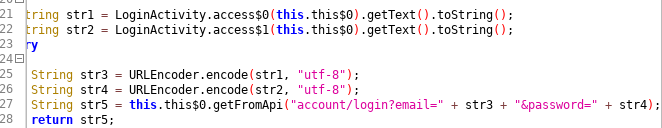
NQ Contacts Backup & Restore is an android app that allows users to backup and restore contact data (as vcard) to/from the remote NQ server. For the audit, the android app was the primary target. Note: The app shares its code base with NQ Mobile Security & Anti Virus - hence the odd class names for a simple contact backup app. Lack of HTTPS usage When logging in or transmitting data, the app communicates with the remote server via HTTP. This can be exploited in various ways. One of these is sniffing the request when a user logs in: As you can see, the username is being transmitted in cleartext. The password is hashed with SHA-1. An attacker can now crack the SHA-1 hash (because that's pretty easy nowadays): Additionally, an attacker could use the sniffed hash to download the stored contacts from the server directly. As described later, the attacker can also access transmitted contact data. Vulnerability type: Plaintext data tran...